The First Line of Defence
Security tools like firewalls are useless if you
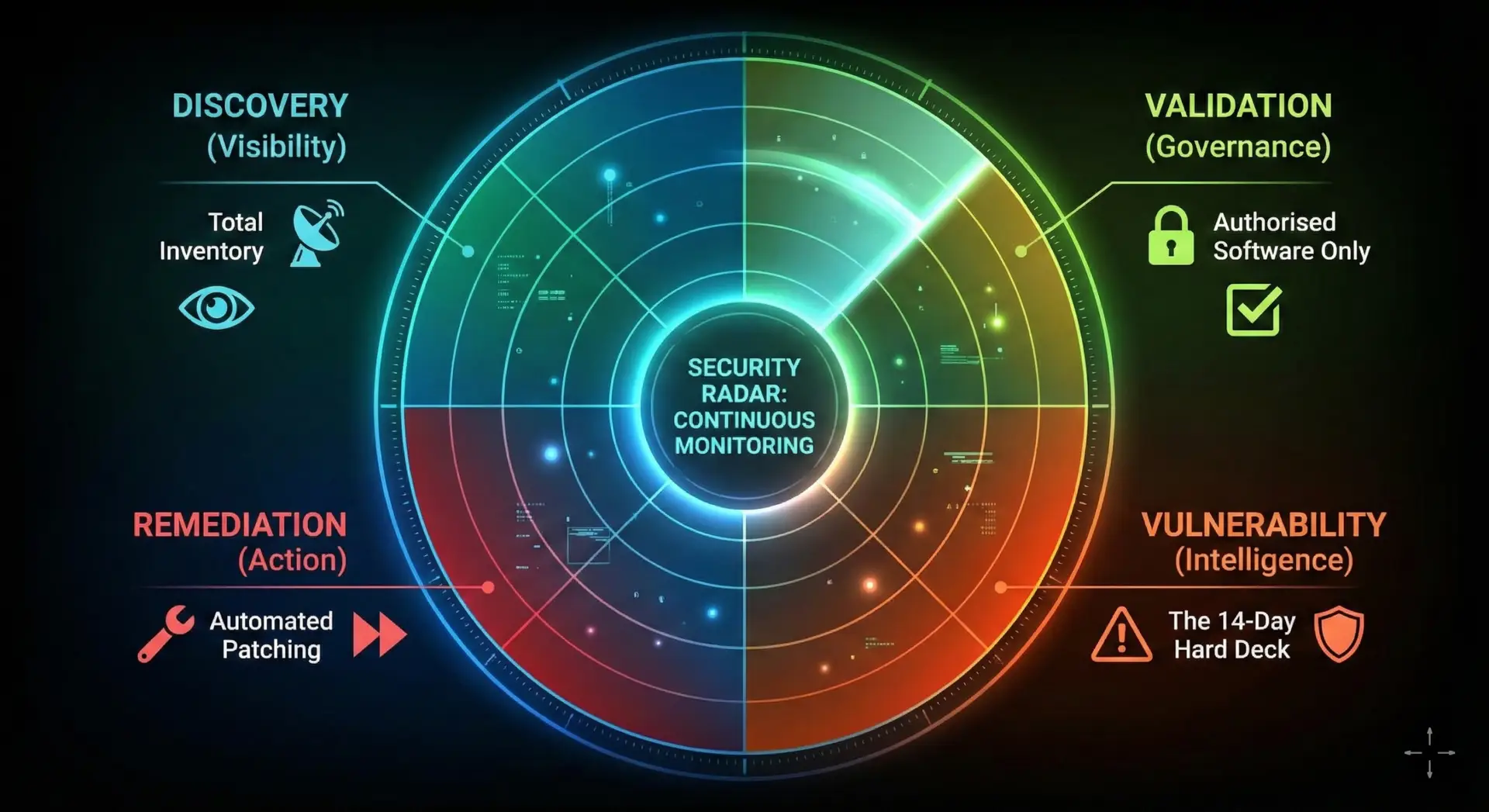
don't know what you are protecting. Taking the view below it bridges the gap between IT Operations and Cyber
Security. Ensuring that the Security Team has a complete trustworthy map of the estate.
The Four Pillars of my Service:
1. The "14-Day
Hard Deck" (Vulnerability Management)
Cyber Essentials Plus requires
critical vulnerabilities to be fixed within 14 days. Make this a reality.
- Automated Patching: Implement tools like Winget to patch third-party apps
(Chrome/Adobe) in the background without user intervention.
- The Zero-Day Response: When a high-risk alert hits,
have the location data ready immediately to target the specific devices that need
remediation.
2. Attack Surface
Reduction (Shadow IT)
Every piece of unnecessary software
is a potential open door for a hacker.
- Ghost Hunting: Identify and remove "End of Life" software that is sitting dormant on the network.
- Unauthorised Apps: Use inventory data to flag "Shadow IT" where users
have installed tools that have not been vetted for security risks.
3. The Single
Source of Truth (CMDB)
Security Operations Centres (SOCs)
often suffer from "Alert Fatigue" because their data is bad.
- Data Unification: Connect the dots between Inventory (SAM TOOLS), Intune
(Management) and Vulnerability Scanners/Defender (Security).
- Context: When an alert fires we can see exactly who owns the device,
where they are located, and if the data on it is sensitive.
4. User-Centric
Security (Culture)
Security policies often fail
because they block people from working.
- Seamless Updates: Configure update rings to respect the user's working
hours. Ensuring that security restarts happen when the user is abile or finished for the
day, preventing the frustration that leads to users bypassing security controls.
- The "Why": Communicate security changes or updates in clear human language so emd users understand they are part of the solution not the problem.